New with Fonolo is the ability to integrate your SAML2 Single Sign-On with the Fonolo Portal.
Single sign-on (SSO) is a centralized session and user authentication service in which one set of login credentials can be used to access multiple applications. The benefit is in its simplicity; SSO authenticates users once on one designated platform, enabling the use of many services without having to log in and out each time.
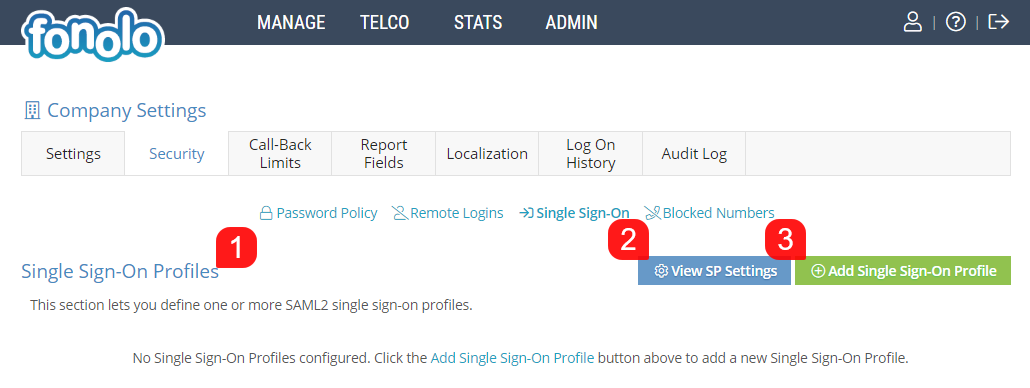
To begin setting up SSO within the Fonolo Portal, start by going to Admin > Security > Single Sign-On.
Single Sign On Profiles
Here, you can view any sign sign-on profiles previously defined within the Fonolo Portal (1). You are also able to view the Fonolo Service Provider (SP) Settings (2). Lastly, you can create new Single Sign-On Profiles by clicking the green button (3) in the top right corner of the page.
 View SP Settings
View SP Settings
As Fonolo is the Service Provider, here you can view the information required to set up SAML2 Single Sign-On.
The Fonolo Single Sign-On URL (1) is displayed at the top, and is https://portal.fonolo.com/saml/.
SP and IdP usually communicate with each other about a particular subject. That subject should be identified through a NAME-IDentifier , which should be in a predefined format so that It is easy for the other party to identify it based on what it reads. This is the NameID Format (2) that Fonolo uses, and it is listed here as well.
Encrypting the SAML2 assertion (3) is optional. In most situations it isn’t encrypted and privacy is provided at the transport layer using HTTPS. However, encryption of the assertion an extra level of security that Fonolo supports, if the SAML assertion contains particularly sensitive user information or the environment dictates the need. You can also download the certificate file (4) as well.
Once all information has been reviewed, you can Close (5) the pop-up.
Add a New Single Sign-On Profile
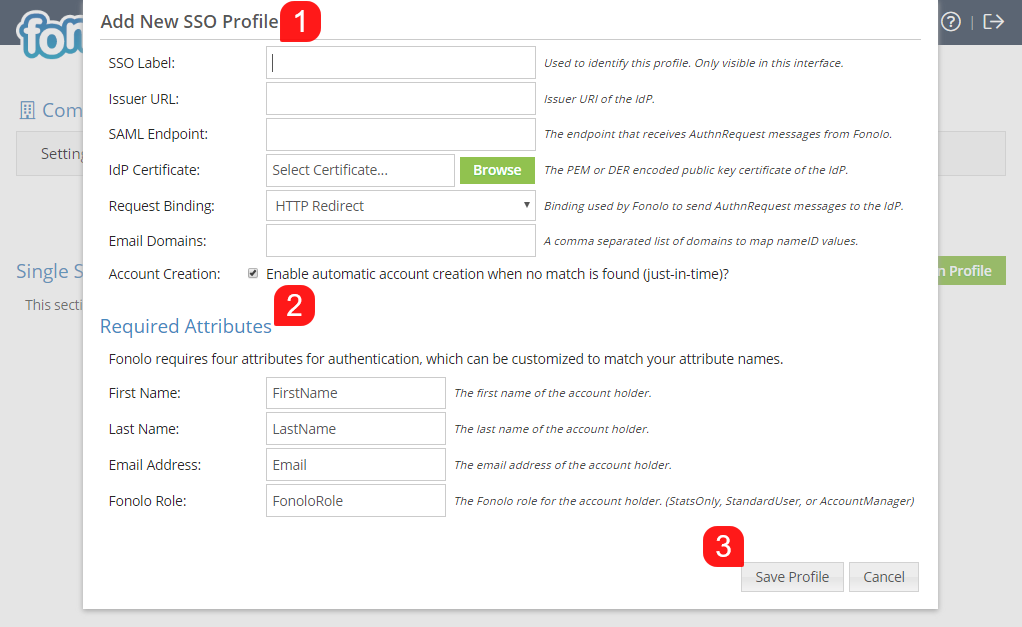
When adding a new SSO Profile to your Fonolo Portal there are several variables (1) that need to be defined.
- SSO Label is used as an identifer for the Profile with the Fonolo Portal, and is only used internally for your own reference.
- Issuer URL refers to the Entity Id of your identity provider, it is a URL that uniquely identifies your SAML identity provider. According to the SAML specification, the string should be a URL, though not all providers respect this. Not required by all providers.
- SAML Endpoint is the address that Fonolo will use for the HTTP Request Binding, whether Redirect or POST is selected. This URL is provided by the Identity Provider.
- IDP Certificate is the SAML certificate that the IdP uses to sign the SAML assertions sent to Fonolo. This can be uploaded by clicking the green ‘Browse’ button. The SAML certificate is usually provided in PEM format from the IdP. Keep in mind that Fonolo will only work with PEM or DER formatted RSA certificates. DSA certificates are not supported.
- Request Binding – There are various types of request binding for SAML2. Fonolo supports the commonly used Redirect and POST binding
- Email Domains – Here, you can specify a comma separated list of email address domains that will be checked against this SSO Profile during login of the user into the Fonolo Portal.
- Account Creation – You are also able to specify if an account should be created for the user upon login, if no account is detected during successful authentication via SSO by a new user.
Required Attributes
Fonolo requires four attributes (2) for authentication, which can be customized to match your attribute names. These are used to update account information within the Fonolo Portal when a user logs in via SSO, and also to create new accounts when the Account Creation option is enabled in the above menu.
The Fonolo Role field cannot be customized – this allows Fonolo to create new accounts with the correct role type (StatsOnly, StandardUser, AccountManager) when required to do so. If no role type is present in this field it will default to StatsOnly for account creation; the account type can then be changed by an Account Manager. Please be aware that if the Account Update option is enabled and no role type is received on login, the account will default to StatsOnly.
Once all settings have been configured, click the green ‘Save Changes’ button (3) at the bottom of the pop-up to save the new SSO Profile.